Consents management, encryption, protection against data breach, anonymization, or passwordless logins are just few examples of what you can do with Ianum® tools
COMPANY ADVANTAGES IANUM FOR USERS
Easily combine our tools to improve your customer data protection. Enjoy effortless integration with your processes. Safeguard your digital assets with our cutting edge technology
Protect your privacy by governing your data and consents. Secure your identity with our anti-fraud authentication system.
Everything from your smartphone
Find out More →

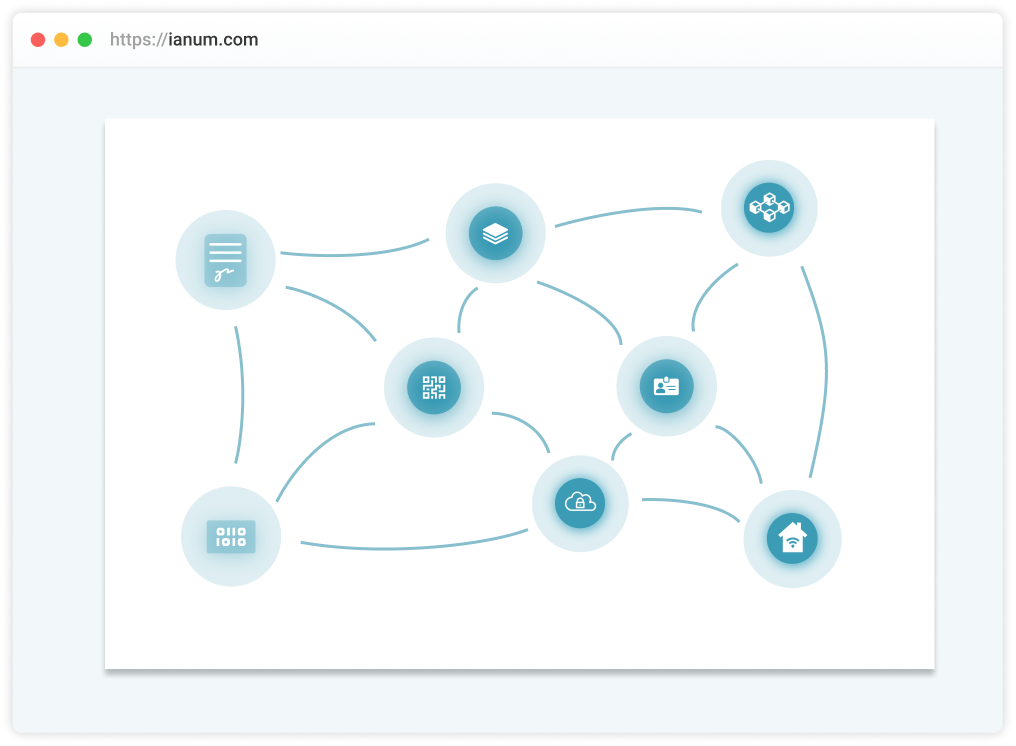
Choose what you need to reach your goals in terms of Privacy and Data Protection: our Privacy by Design components will make your goal easier.
Consents management, encryption, protection against data breach, anonymization, or passwordless logins are just few examples of what you can do with Ianum® tools.
While allowing strong authentication with data protection, Ianum is a flexible platform made of tools you can connect.
Currently they're used in different scenarios, from internal employees authentication to eCommerce secure login.
Try with two of the most used out-of-the-box examples: website login and newsletter subscription!
We have set up a demo website where you can try our login solution, safely sharing your name and email
GO TO LOGIN PAGEEnter your email to stay up to date with out latest news, using Ianum to manage your subscription
Smartphone based authentication without the boredom of passwords

Passwordless login for SAML 2.0 compatible business applications

Directly manage your customer consents, anonymizing them

Users can safely share personal information, stored protected and encrypted

Protect confidential tokens and informations generated by users on your services
Encrypted storage space where you can store any binary file

Store cryptographically signed timestamp proofs on public or private blockchains

For countries adopting it, Ianum will be able to manage your Digital Identity

Control data produced by IoT devices, and safely manage ownership
REQUEST A DEMO
Get a free 30-mins demo to see what Ianum can do for you, for your business and for your customers
REQUEST A DEMOMake your choice among our integration solutions and integrate Ianum® within your processes with just few simple steps.
Let your users adopt our public App to interact with your Ianum® integration
Include Ianum® in your smartphone App or Backend Logic and improve user experience
Fully customize your Ianum® connection calling directly our API REST endpoints
Onboarding means registering the user for the first time, collecting some basic information, and asking them to accepts agreements such as Terms and Conditions of your services or Marketing newsletter. You can manage all this process using Ianum® Passwordless Authentication.
You have a set of agreements your users signed: when they first registered, when they purchased a new service, etc. Over time you update them and users have to accept new ones. Integrating Ianum consents management, you can do everything automatically.
Manage employee access within company services is crucial. Emails, HR platform, internal applications: each company has a huge variety of software. Managing employee access with a central identity provider is the key of success.
Event registration is the heart and the first point of contact of an event. Providing secure and mobile-responsive event registration is the key to success. Ianum is a great solution for mobile registration.
Adopting Ianum® within your processes guarantees you are GDPR compliance in users’ data management
Ianum® has been built with privacy in mind. No one can read your users' data, not even our developers, making it a trusted secure tool
Everything is built with encryption and cryptography in mind, to ensure data can be decrypt only by the owner of the key
We hold encrypted data, you hold the keys. In this way, massive data breach are impossible to become reality
We are compliant with all the main infrastructure and development security standards such as SOC 1 / 2 / 3, PCI, ISO 9001 / 27001 / 27017 / 27018
You decide where to store all your data managed with Ianum, whether on our cloud available locations or on-premise
Our partners offer a diverse array of expertise, skills, resources and technologies to ensure the success of our mutual customers. The Ianum® Partner Program provides the resources and support to help you engage and connect with your customers, building privacy-first tools based on Ianum® Platform

ReD Open S.r.l.
STRATEGIC ALLIANCE PARTNER
Leader in the innovators’ ecosystem, ReD Open is commited to corporate sustainability by valuing the responsibility of data governance in decision-making.